Eliminate known DNS and TLS problems that put your security and compliance at risk.
Multiple, known weaknesses in the internet chain of trust put enterprise data security at risk. This white paper identifies 9 issues with DNS and TLS that organizations need to understand and address to ensure data is secure and customers are protected.
The Digital Chain of Trust is Broken
Digital transformation is driving unprecedented expansion of the enterprise digital attack surface. The number of network endpoints is growing exponentially. Deloitte cites the World Economic Forum Global Risks Report, 2017, saying:
Digital technologies and innovation are growing exponentially, accelerating cyber risks, new attack vectors, and greatly expanding the attack surface that organizations must patrol and defend.
Deloitte, Take the lead on cyber risk. 2017 →
The explosion of data volume and endpoints is creating significant challenges for enterprise network IT teams. Enterprise reliance on DNS and TLS integrity is critical as attack vectors proliferate. Security experts agree: “BGP and DNS are the soft underbelly of the web,” says Alan Woodward, Professor of computer science, University of Surrey.
Network endpoints are where proprietary enterprise and customer data
is captured, processed and set in motion. For enterprise, data-in-motion security relies on flawless implementation and monitoring of DNS and TLS protocols to ensure the Chain of Trust is maintained.
Digital business services run on the Domain Name System (DNS), which is the network foundation for all digital communications, customer engagement and digital service delivery. Enterprises must secure it, or they will be dangerously exposed to compromise.
DNS and Transport Layer Security (TLS)
The DNS is known to have security exposures due to under-utilization and enforcement of DNS security extensions (DNSSEC) and poor management controls over connections equipped with Transport Layer Security (TLS) encryption and authentication. While DNSSEC and TLS encryption promise a foundation of security, management shortcomings i.e. legacy tools, outdated processes and human actions create exposure. Data security and compliance need revisiting, particularly as DNS networks scale.
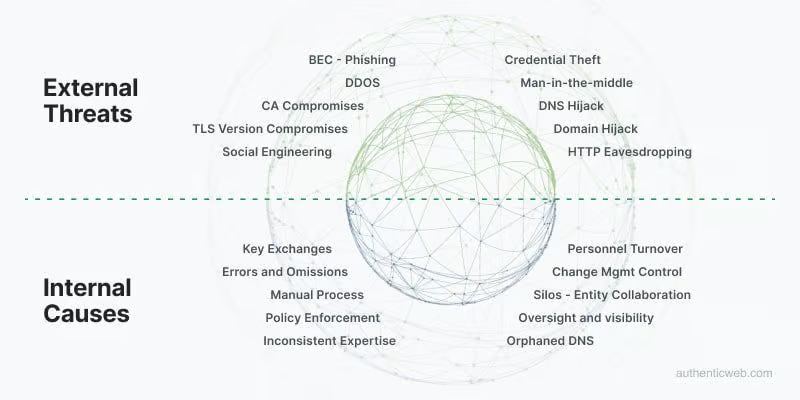
Enterprise DNS network security weaknesses largely exist due to processes, systems and operations where human error and omissions occur. Enterprise systems and management processes tend to operate in silos. Lack of visibility, control and compliance over the actions and inactions of personnel are the primary source of network security vulnerability. The lack of compliance over internal, partner, and supplier network parties creates weaknesses in the Chain of Trust, which expose the business.
Independent research validates that the biggest security risk to enterprise is the reliance on people, operating in silos with legacy tools, and inconsistent expertise and motivation, exposing the enterprise to TLS and DNS security risk.
TLS and DNS: The Frontline of Enterprise Data-in-Motion Security
TLS and DNS technologies underpin enterprise digital infrastructure as the frontline for network data-in-motion security. Transport Layer Security is the trust protocol to authenticate communications between multi-party systems and to encrypt data in motion. The Domain Name System (DNS) is the addressing technology used as the address book of the Internet, directing/ routing data between network endpoints.
Silos between network edge, endpoint and data security systems can restrict an organization’s ability to prevent, detect and respond to advanced attacks.
Gartner: Best Practices for Detecting and Mitigating Advanced Threats. 2016 Updated March 2016 →
Enterprises utilize myriad third-party vendors for TLS relying on internal human resources and Certificate Authority (CA) employees to establish and maintain network security. With disparate employee groups, siloed systems and manual processes, it is practically impossible to maintain control and visibility over the risk factors that can compromise the Chain of Trust for data in motion. This represents a data security and compliance weakness.
