End-to-end business lifecycle processes are a lot like ballistics: being off by a wee bit on the front end makes for a huge miss on the target of the projectile’s journey.
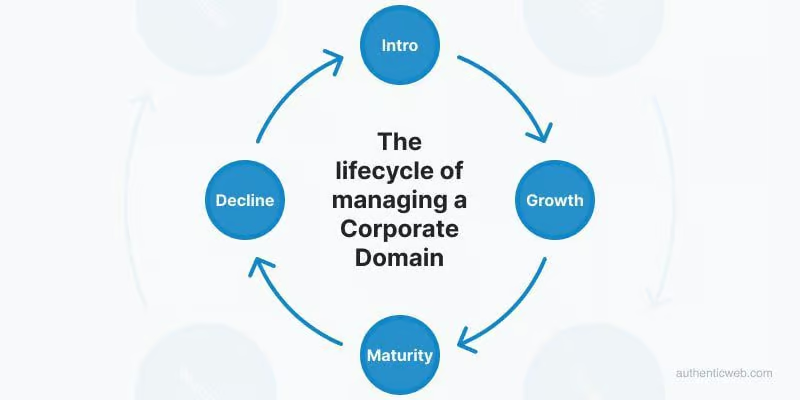
And so, it is with the lifecycle of managing a corporate domain. Much of the pain of managing corporate domains throughout an organization can be traced to the outset of the domain journey where errors and omissions begin.
Registering or introducing a new domain starts with a role we call “the originator.” She/he may be a marketing manager setting up a time-limited campaign in need of a customer-facing URL. New products require domains for brand and promotional purposes. A typical new pharmaceutical product often registers a score of domains, with generic Top Level Domain (TLD) and country code TLD versions for various market jurisdictions (newdrug(dot)us/ca/de/cc, etc.) In-house legal counsel seeking to protect corporate brands and intellectual property may insist upon registering common misspellings and preventative-use domains, e.g. www.newproductsucks.tld
Large organizations operate in silos with many originators. Each is advised to follow a defined process to make sound decisions and prevent all manner of domain-related errors and omissions throughout the domain lifecycle.
Every new domain requires up-front considerations:
- What domains and TLD variations are required for a particular digital initiative?
- Why not use a sub-domain? (www.newdrug.brand.com)
- Is the domain temporary i.e. a seasonal campaign? Should it re-direct on a given date?
- What is the ideal renewal term? Should it auto-renew or expire, and when?
- Are special domain services required, such as registry lock or WHOIS privacy?
The list of domain details is much longer than the above and there is another key role we call “the approver.” Approvers are often more than one person. A marketing manager has a chain of supervision, perhaps to the Director or VP level for a new domain request approval. Legal often signs off on the brand approval, including trademark or copyright considerations. IT pre-approves that the domain can be hosted. Finance may initial the budget or departmental charge-back for the cost of the domain(s).
Myriad originator and approver tasks add up to a complex process. Surprisingly, most organizations lack a formal process or system to manage change, relying instead on email threads and shared knowledge of how things ought to get done. Even where policies are defined, they’re often managed by a key knowledge role such as “domain administrator.” These folks can be terrific and typically operate with IT support. The pain starts when they’re not available or get left out of the decision-making loop. Invariably these subject matter experts turn over leaving knowledge gaps in this critical area.

Not every organization is oblivious to the risks of relying upon manual processes or sole subject matter experts. For many F1000 brands domain management pain has been the mother of invention. Some have created process forms hosted on company intranet sites with instructions. Others have scripted SharePoint applications to guide originators and approvers through a repeatable, compliance-oriented process for ordering new domains. While some process automation is arguably preferable to none at all, these in-house solutions have their own disadvantages. Firstly, they’re not free. Bespoke systems require up-front development investment, ongoing maintenance costs plus overhead. In-house systems tend to be rigid and inflexible. As user needs evolve, the internal technical debt and workarounds accumulate. Also, most front-end systems lack integration to the domain registrar vendor systems and/or the internal DNS network management environments. Domains are easy for originators to order but a massive ongoing task for the organization to govern and change-manage over time.
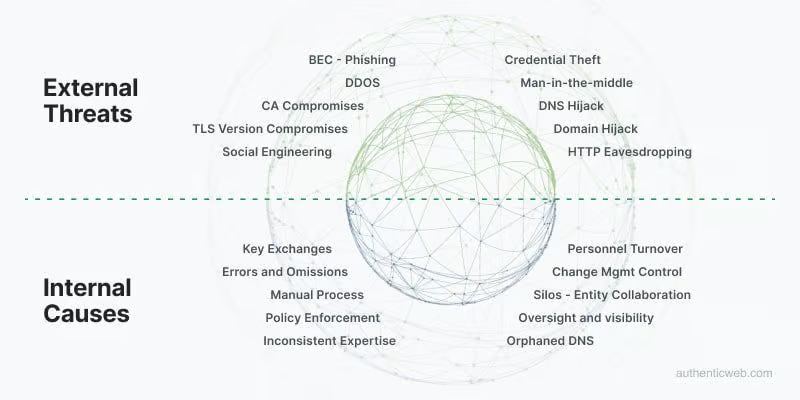
Once a domain is registered, most front-end processes are done. That places a domain in the limbo of ongoing governance, beyond the scope of origination/approval. Few, if any front-end management applications follow domains through their complete lifecycle. Examples abound of enterprises with “orphaned” domains and subdomains, forgotten by long-departed originators and IT support individuals. Orphaned domains are prime targets for hijacking and misuse. Malicious parties are known to scour the corporate DNS landscape for these easily compromised “loose-end” domains and their associated DNS resource record settings.
Domain registration front-end processes are either manual and error prone, or partially automated e.g. using SharePoint or similar, and severely limited in needed functionality, operating as a silo vs. a true end-to-end process.
Origination and approval are internal processes. The critical external factor involves vendors in the domain management operation: domain registrars and managed DNS vendors. Pain comes to organizations that use multiple registrars and DNS providers. Every registrar has its own administrative environment, login process and password regime. Some employ 2FA and Single Sign On access controls. Many don’t. Some provide account service representatives while others are purely online. Mapping and training a large, corporate originator/approval process to multiple, disparate external registrars is difficult, if not unfeasible. Over 600 companies including Mastercard, Hilton, and ING Bank experienced severe domain pain in this multi-registrar scenario when orphaned domains in their portfolios were hijacked in the infamous Spammy Bear attack. Most of them used a primary registrar, but the hijacked, orphaned domains were registered elsewhere. Process hates confusion. Managing multiple registrars creates cost, security risk and compliance gaps.
Domains once ordered and set up require ongoing scrutiny and governance. Are the domains still needed? Are they set up correctly on the DNS? Have they been re-directed or modified to include subdomains? Were they configured with security measures such as SPF, DMARC, and DNSSEC and are the resource records functional? These and other basic governance checks are notoriously painful to manage when the originators, approvers and IT resources are long-gone owing to turnover and the passage of time. Organizations simply forget the domains they ordered, operate and why. Old, potentially forgotten domains and subdomains are the ideal playground for malicious parties who target this exact environment. The most security-conscious companies in the world have been hacked via their legacy domains. An integrated, end-to-end domain management system shouldn’t just make the origination and approval process tighter. It should follow each and every stage of the domain until end of life, which could be decades. Only a fully integrated change management system can hope to meet the necessary standards for efficient and secure domain management. Effective, pain-free domain management requires tamper-proof audit capabilities and enforced compliance governed by configurable business rules. Manual and home-grown change management systems fall far short of these requirements.

