In a digital world, organizations and individuals rely on the internet daily for a limitless number of essential tasks. Internet users count on organizations to maintain online service availability and to protect their data privacy. Users need to be able to trust that digital brands are authentic i.e. that brands are who they say they are. Unfortunately, digital brand trust is increasingly threatened by vulnerabilities in the internet’s very foundation: The Domain Name System, or DNS.
Every single online action starts with the DNS. Whether for shopping, banking, paying a tax bill, or connecting with an enterprise service delivery system — any browsing purpose at all — the DNS directs requests to the online destinations, content and applications sought by users. The DNS is absolutely central to the internet and how it operates. It is this very criticality that has made the DNS vulnerable to abuse. Hijacking, spoofing, man-in-the middle attacks, and other threats that can disrupt an organization’s online operations with disastrous consequences for brand reputations and user security.
Domain Name System Security Extensions, or DNSSEC, helps defend against DNS security threats. Unfortunately, many organizations choose not to adopt DNSSEC because it’s difficult to set up and manage.
Traditional, manual practices for DNS management and the common practice of using multiple DNS services have made DNSSEC deployment cumbersome, inefficient, and costly. There is a solution: consolidating all domains and DNS services under a unified, automated environment can simplify and secure organizations’ at-risk internet operations.
In this guide to DNSSEC, we’ll explain what DNSSEC is, how it works, and why it’s important. We’ll identify the obstacles to implementing DNSSEC and show how a simplified approach to DNS management makes effective deployment possible. Without DNSSEC, organizations and their users are increasingly at risk.
In this guide, we are taking a deeper dive into DNSSEC.
Domain Name System Security Extensions, or DNSSEC, helps defend against DNS security threats, specifically related to Man-In-The-Middle (MITM) and DNS Hijacks. While DNSSEC is extremely effective, many organizations have not yet adopted it simply because it is challenging to set up and manage over the lifecycle of a domain and the larger portfolio of domains.
Traditional, manual practices for DNS management and the common practice of using multiple DNS services have made DNSSEC deployment cumbersome, inefficient, and costly. There is a solution: consolidating all domains and DNS services under a unified, automated environment can simplify and secure organizations’ at-risk internet operations.
In this guide to DNSSEC, we will explain what DNSSEC is, how it works, and why it’s important. We will also identify the obstacles to implementing DNSSEC and show how a simplified approach to DNS management makes e
What Is DNSSEC?
DNSSEC is a security protocol that validates DNS query results. It protects internet users (clients) from forged DNS data (resolvers.) It uses tamper-proof, digitally signed keys to verify the authenticity of online destinations. It’s like a digital handshake that confirms two parties are who they claim to be.
Understanding what DNSSEC is requires looking at the DNS itself. The domain name system was developed in the 1990s as a way to make the internet easier to use. It’s often described as a directory that translates the words we type into a browser into an IP address where content is served. For example, apple.com is an easily remembered domain. The DNS translates the domain (URL) to an internet protocol (IP) address on the server(s) where Apple’s website is found – in this case 17.254.0.91. The DNS makes browser-based address queries significantly easier than an unwieldy list of millions of numeric IP addresses.
Ease of use and ubiquity are contributing factors to the evolving risks associated with the DNS. As the internet matured, it became apparent that there were many ways to abuse and misuse the DNS for malicious purposes. The DNS isn’t very secure. For years, malicious parties have become inventively adept at compromising the DNS, by intercepting, forging and/or manipulating DNS query responses. As a result, internet users and organizations cannot always be sure that online content requested is in fact from a legitimate, authenticated source. This can be very dangerous.
DNSSEC was the industry response to the authentication vulnerabilities inherent to the DNS. It was developed by the Internet Engineering Task Force (IEFT) in the 1990s to counter the "impersonation" problems associated with the DNS. DNSSEC’s dual-encrypted signature keys ensure that the online content internet users request through their browser clients returns legitimate, authenticated results from the Domain Name System. Without DNSSEC, organizations are vulnerable to their DNS systems (and customers) being compromised.
How Does DNSSEC Work?
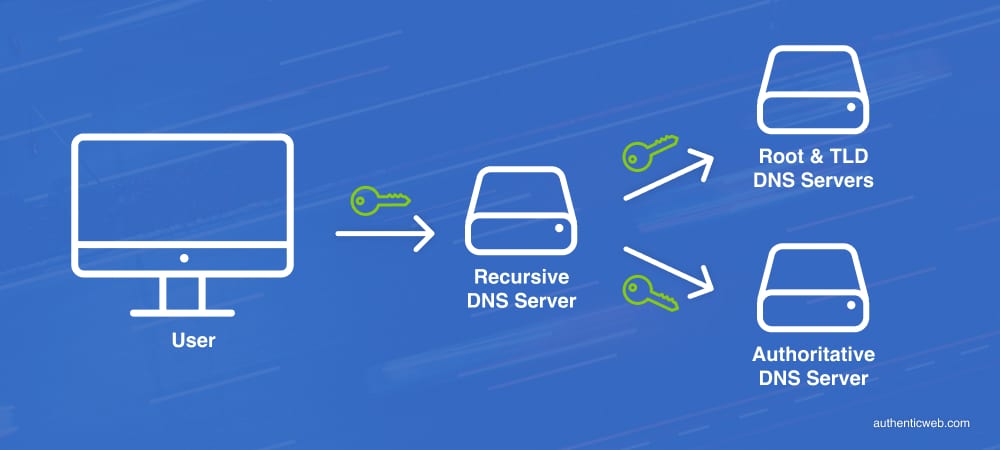
The DNS is organized into zones and uses resolvers to direct browser-based queries. To protect DNS zones, DNSSEC matches two digital keys, one public and one private. Together, digital signing (DS) keys validate the authenticity of DNS data. Cryptographic signatures ensure that DNS resolvers are locating the legitimate IP destinations instead of hijacked or cache-poisoned DNS zone files. Keys themselves are signed as part of the chain of trust.
The private key is known only to the domain owner. When DNS data is requested a DSKEY is used to "sign" the data. The recursive DNS server compares the signature to the public key in the registry records. If the two match, the internet user receives the records that point to a host and gains access to the website. If they’re different, the records are assumed to be a forgery and the DNS data is dumped.
DNSSEC offers brand protection by ensuring internet users will not be misdirected to unauthorized online content destinations. Online shoppers visiting gucci.com have every expectation of being at the real Gucci website. Likewise, banking customers certainly want assurances that their online transactions are taking place at the authoritative bank website rather than a fraudulent imposter site designed to intercept and steal their vital information. DNSSEC assures internet users that requested online destinations are those of the legitimate owners.
What Happens Without DNSSEC?
Without DNSSEC, organizations are exposed to the risk of DNS hijacking, or "spoofing" by a number of means including cache poisoning. DNS recursive servers operate more efficiently when they store DNS query data for repeated or similar DNS queries. DNS cached data can be compromised and modified so as to return a falsified response to a DNS query.
Once a user is misdirected to an unauthorized server (IP address), their computer is open to malicious content like malware and viruses. It’s particularly insidious when hackers can impersonate a legitimate website, complete with SSL certificate encryption to dupe a user into logging in, believing the website or application to be legitimate. DNS hijacking can and has resulted in stolen data and credentials.
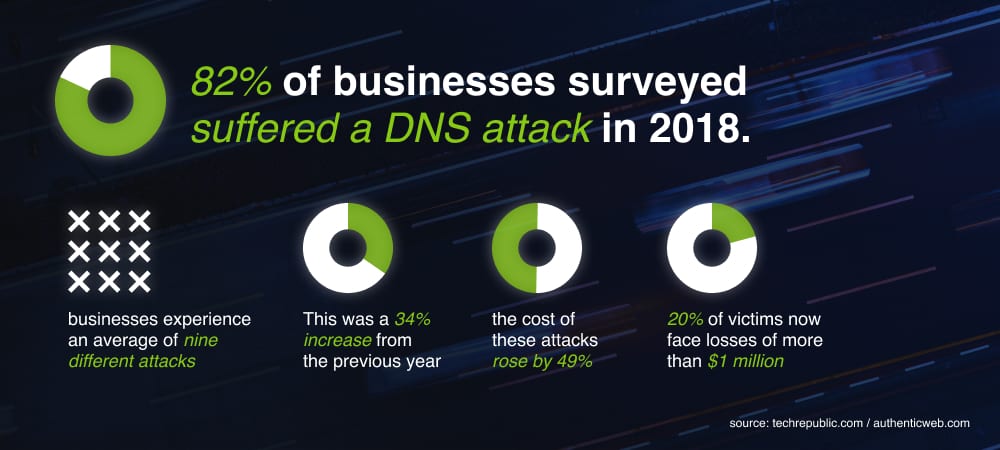
DNS attacks are increasingly frequent and costly. According to a global analysis, 82% of businesses surveyed suffered DNS attacks in 2018 averaging nine different attack types – a 34% increase over the previous year. The cost of these attacks rose by 49 with 20% of corporate victims losing over $1 million per occurrence.
A company’s online presence is crucial to its financial performance. DNS attacks can disable websites, interrupt sales, and trigger the loss of loyal customers. Brand reputation can suffer, exacerbated by lawsuits and regulatory penalties. Organizations that ignore DNS defenses like DNSSEC place themselves, and their users, at significant risk.
Every sector is vulnerable to DNS compromise, but malicious parties go where the money is, making some industries particularly exposed. Financial data such as banking information, credentials or credit card records are lucrative spoils to hackers. Organizations that store payment data in industries like finance, banking, healthcare, and online payment services are at high risk. Government and membership-related services such as hotel loyalty programs are frequently targeted by DNS attackers.
Why is DNSSEC Not Used More Widely?
DNSSEC is proven to be a reliable defense against DNS hijacking, yet many organizations have not deployed it. Two factors influencing the lack of broad adoption are the complexity and cost of effectively implementing DNSSEC.
- DNSSEC adoption is complicated and costly because of the way companies manage their external DNS. Most enterprise-level organizations use multiple registrars and often dozens of DNS services due to legacy decisions dating back decades. Because many DNS providers don’t support DNSSEC, and rarely integrate with registrar systems, deployment can be inconsistent or unfeasible for large parts of a company’s domain portfolio.
- DNSSEC requires a fully coordinated chain of trust for each domain query. Domain registrars, DNS providers, and domain registries each contribute to the chain of trust supporting DNSSEC. With so many parties in the mix, consistent, low-effort administration of DNSSEC across a large domain portfolio becomes challenging.
Those are the external challenges. Internally, organizations often lack sufficient expertise to correctly implement DNSSEC. The steps to setting up DS keys and RRSIGs at your DNS service and ensuring they’re in sync with domain registrars and registries are typically manual, involving significant staff effort and resources. Additionally, these keys roll over each year, so the oversight must be maintained over the lifecycle of every domain.
To validate the correct operation of DNSSEC, it’s necessary to constantly check that digital signing keys are present and valid. It’s a formidable task. It requires checking the domain zone file to verify that the RRSIG and DS records are present and correct. Tools like Verisign’s DNSSEC Analyzer can be helpful for single domain lookups but are less useful for those administering hundreds or thousands of domains. Further complicating the process, a lookup tool may confirm that digital signing keys are present even when the DS key has expired or the RRSIG has been changed. To maintain DNSSEC authentication, all keys have to be individually tracked and renewed.
Given all the moving parts, it’s easy for organizations to assume DNSSEC is actively working when, in fact, a broken link in the DNS chain of trust has invalidated the authentication.
The most effective way to administer DNSSEC is within an integrated, end-to-end change management system. Otherwise, it can be misconfigured or operating with expired keys that offer no protection at all.
How to Implement DNSSEC
The biggest problem with DNSSEC isn’t the protocol itself. The real problem underlying its apparent cost and complexity is the inherently inefficient DNS management due to manual, legacy processes.
Integrating DNS management will make DNSSEC easier to implement. More important, it will make DNSSEC easy to monitor and maintain so you can gain ongoing security benefits for your organization and keep your customers safe.

The first step in securing your DNS network is to conduct an APEX-level DNS audit. Identify all domain registrars and DNS providers. Survey the pass/fail status of DNSSEC on every domain. Similarly validate other DNS security measures including: DMARC, SPF, DKIM, and TLS/SSL certificates on all domains and re-direct domains. An audit report can identify DNS security weaknesses across an entire domain portfolio.
Every domain and its associated DNS zone file require common compliance policies, including rules for DNSSEC. Organizations should codify their policies such that every domain (out of hundreds or thousands) is subject to a consistent security standard. Inconsistencies in the use of Start of Authority (SoA), SPF, DMARC, and DNSSEC are gaps in your DNS security posture that malicious parties actively target and exploit.
DNSSEC is prohibitively complicated when companies use multiple providers and platforms such as domain registrars and DNS services. If a DNSSEC test turns up an invalid DNSKEY, for example, the administrator has to choose the specific DNS admin portal to log into to remediate the issue. Multiply this task by hundreds or thousands of domains across dozens of DNS providers, and change management becomes a time-consuming and costly nightmare. Consolidating to a single domain registrar DNS provider that both support DNSSEC will centralize DNS security and simplify DNSSEC implementation and maintenance.
Instead of using multiple, disconnected administrative systems for domains, SSL certificates, and DNS-related tasks, implement a unified change management system that integrates domain registration and DNS management under a single, secure management interface. When you do, ensure that DNSSEC and other DNS security measures are standard operating features within the system. An integrated, end-to-end management suite offers secure access to change management — a single source of truth for all elements and a centralized management hub to make changes.
Summary
DNSSEC is a highly recommended DNS security measure because it authenticates DNS queries, effectively preventing DNS hijacking and cache poisoning, two ongoing and serious cyber threats. But effective DNSSEC deployment demands efficient DNS management.
When you’re ready to streamline your DNS and domain management with a platform that supports DNSSEC, reach out to our team. We can help you discover the security and management issues within your own organization and work with you to determine a solution.