The domain management lifecycle may start with a business originator but it’s safe to say that IT owns at least 80% of the journey thereafter.
Registering a domain is easy. Setting it up and operating it securely over its lifecycle is another matter entirely. IT owns that show and for most IT folks it’s painful. To be fair, the domain management journey is easy for organizations that own just a handful of domains. Competent IT network administrators with DNS expertise can easily keep track of a small set of domains and their respective DNS settings, SSL certificates and security configurations.
IT pain escalates at enterprises that own hundreds or thousands of domains. The complexity of operating and system silos inherent to these organizations makes errors, omissions and dangerous security gaps not just prevalent but unavoidable. Ongoing surveys bear this out: over 70% of the F1000 have failed to establish basic DNS security practices such as DNSSEC despite the known rise in DNS breaches and compromise.
4 Challenges faced by IT
1. IT Administrators Don’t Control the Registrar Vendor Decisions

Large organizations typically use more than one domain registrar and have several – even dozens of active DNS services. Managing complex network settings across multiple vendor platforms is difficult. Each service has its own administrative control interface. Access controls such as SSO and 2FA differ from vendor to vendor or are absent altogether. Almost no registrar, DNS, or SSL certificate providers integrate with one another or an enterprise change management environment. IT is left to manage these fragmented and siloed vendors and systems landscapes with all their operational challenges. IT must own and control change management to be secure and compliant.
2. End-to-end Change Management Systems Are Not in Place
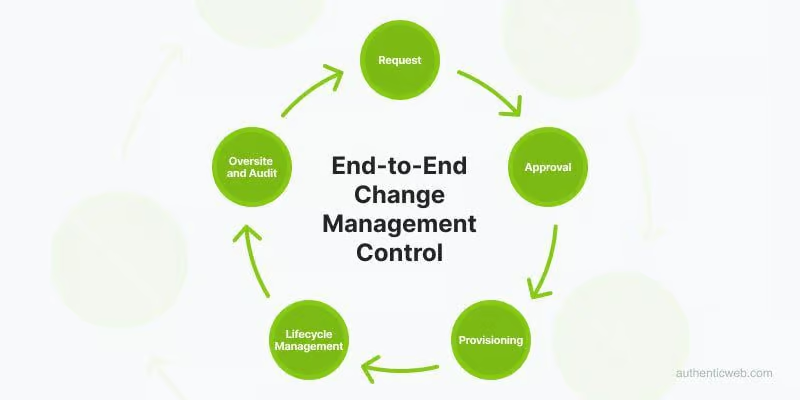
Domains, DNS, SSL certificates and DNS security settings such as SPF, DMARC and DNSSEC require extraordinary attention to myriad details. Overlooking or mismanaging the smallest item will expose the organization to security risk. Examples abound: SSL certificates expire, DNSSEC keys roll over annually, and domains and sub-domains are often forgotten and can be appropriated by malicious parties. Internal staff though neglect, error, or malicious intent can easily change domain and DNS parameters, undetected by network management oversight. The situation persists because domains, DNS, and SSL certs are invariably managed via manual processes, lacking permissioned access, change approvals, audit histories and real-time alerts when changes are made.
3. The Landscape is Complex and Painful to Manage

Domains, the DNS and recommended security practices have evolved extensively in the three decades since the first domains were registered. Basic domain services include various WHOIS privacy, registrar and registry lock and other services, often overlooked by domain registrants, leaving their valuable digital assets vulnerable. Many vendors fail to keep abreast of minimal acceptable password security controls. Accessing a company’s domain portfolio and DNS networks can be as easy as placing a phone call to a retail registrar call center to execute social engineering scams. DNS security measures such as DNSSEC are recommended, but the processes for implementing and maintaining DNSSEC integrity is complex without automated tools. Standards are inconsistent; some DNS service support DNSSEC and others do not. Even the trusted SSL certificate has become a source of management pain. Certificate authorities have been compromised, and fake certificates have been fraudulently represented in hijacking schemes. Even the most diligent SSL certificate managers often fail to encrypt re-direct domains that provides an attack vector for nefarious actors.
4. DNS Audits Don’t Happen and Don’t Work
Financial accounting systems are extremely complex, requiring audits to meet the satisfaction of internal and external audit authorities. Domain, DNS and SSL control practices are equally complex, making periodic audits a good idea. Few organizations are comprehensively aware of the state of their DNS network in real-time or have audit histories required for regulatory compliance. Management may mandate a DNS audit from time to time, yet this process is prohibitively laborious to execute, requiring weeks or months of exhaustive diligence and staff commitment – all while dynamic changes are changing the baseline DNS records. Large domain portfolio owners often launch audit projects only to abort them mid-course owing to competing priorities. DNS hackers are fully aware of the vulnerabilities in most organizations’ DNS systems and routinely target those networks that fail to conduct ongoing, effective audits.
IT teams face two issues that make domains and the DNS painful to manage:
- The landscape is complex, and increasingly exposed to serious security threats.
- The internal environment is under-managed owing to a lack of automated, tamper-proof change management systems spanning the complete domain and DNS management lifecycle.
IT operations face increased security mandates, accumulation of project and operational deliverables, often paired with cyclical budget freezes or reductions. Domains, DNS and TLS management remains a constant drain on operational resources to manage effectively and securely.
As credible domain and DNS security agencies continue to call for increased enterprise security measures, organizations need to honestly assess whether their internal management practices meet a modern standard of compliance. In the absence of automated change management systems, it is very likely they do not.

